Executive Summary
TorZon Onion operates as a decentralized cryptographic platform hosted entirely within the Tor network. Established to facilitate the secure exchange of digital goods and privacy-centric services, the platform utilizes advanced onion routing to obfuscate physical server locations and participant metadata.
Observers note that the infrastructure was designed with a strict utilitarian approach, prioritizing low-latency connections and deep integration with cryptographic validation tools. Unlike traditional web applications, the architecture entirely bypasses standard DNS systems, requiring specialized software to resolve its internal routing paths.
Historical Timeline
Network Initialization
Initial beta testing of routing protocols commenced, focusing primarily on establishing stable connection nodes. The earliest iteration featured a rudimentary interface designed strictly for load balancing and basic cryptographic handshakes.
Multisignature Integration
The implementation of advanced multi-signature (multisig) transactions fundamentally altered the platform's security dynamic. This update required consensus between independent cryptographic keys to finalize network operations, significantly mitigating single points of failure.
Distributed Mirror Framework
In response to increased network traffic and coordinated denial-of-service disruptions, the architecture was segmented into multiple independent routing paths. This distributed mirror system allowed for sustained uptime by decentralizing access nodes.
Technical Architecture
Cryptographic Escrow
Traditional centralized holding mechanisms are replaced by rigid escrow protocols. Funds are temporarily cryptographically locked until mutually agreed conditions are met by participating nodes.
Mandatory PGP
All communications, authentication requests, and transactional metadata are strictly processed through Pretty Good Privacy (PGP) frameworks, ensuring end-to-end operational confidentiality.
Walletless XMR Focus
The platform champions a walletless architecture utilizing Monero (XMR). By eliminating on-platform digital balances, the system minimizes the economic risk associated with server compromise.
Interface Documentation
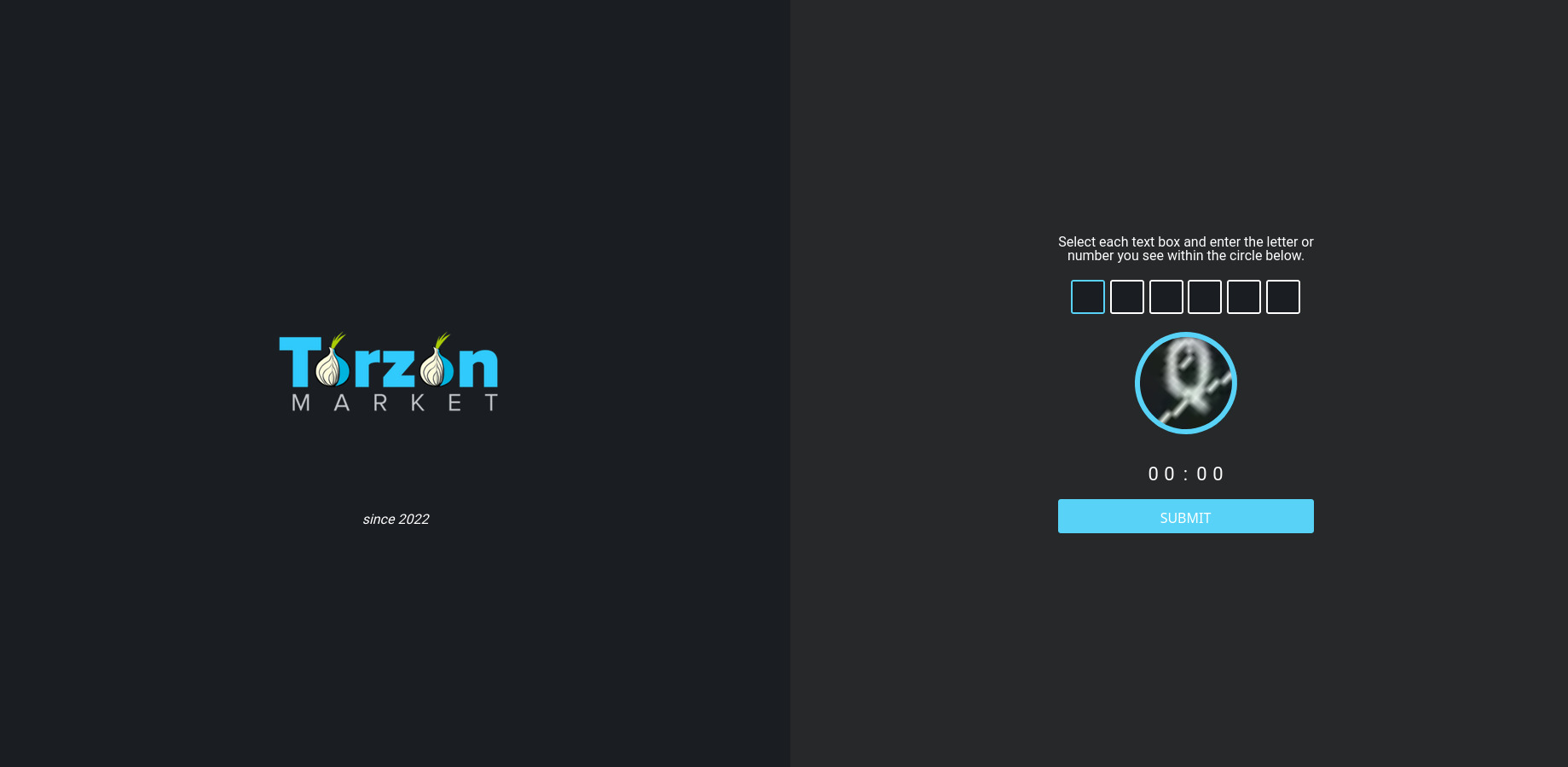
Fig 1. DDoS Protection Screen
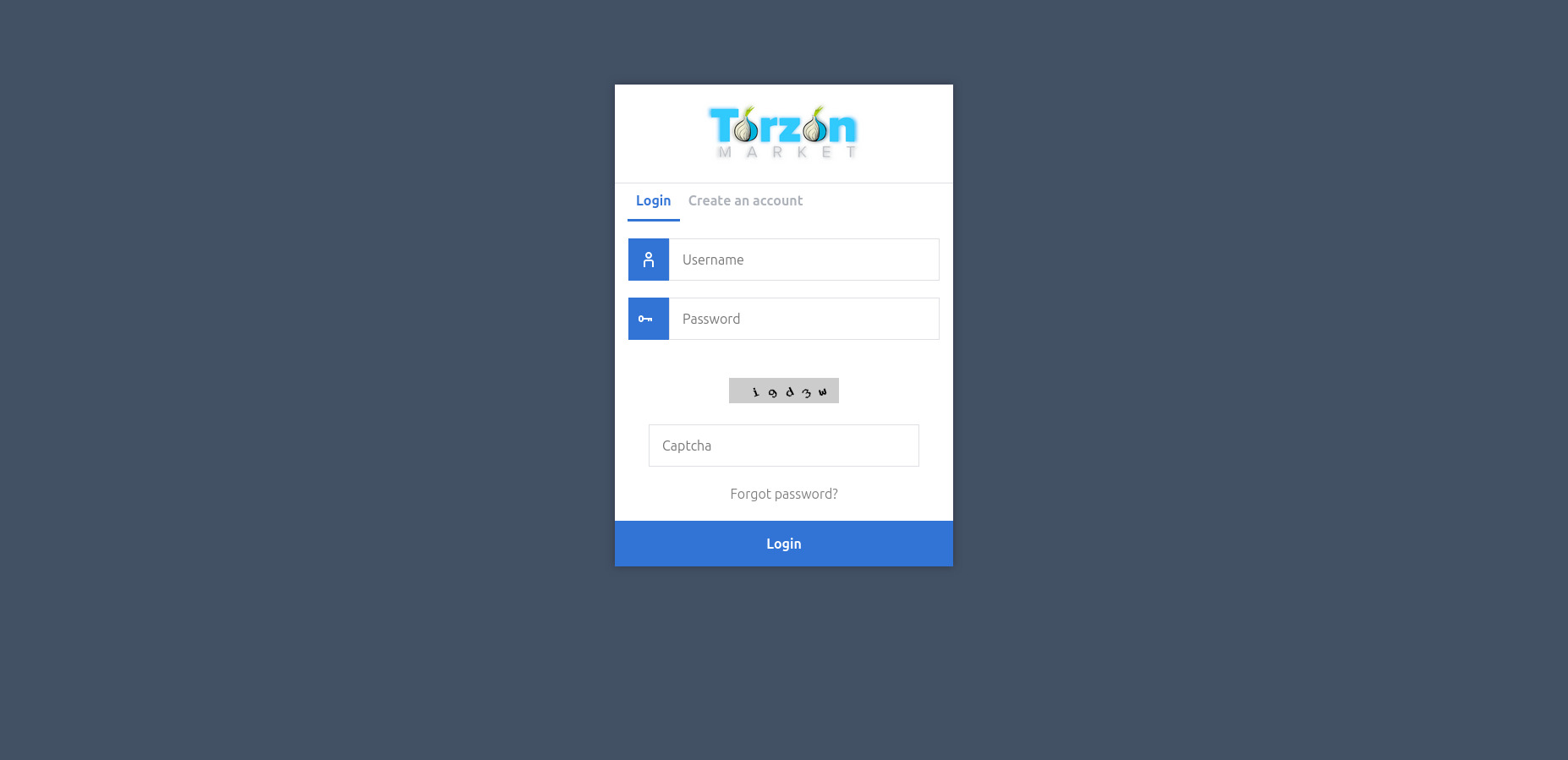
Fig 2. Encrypted Login Interface
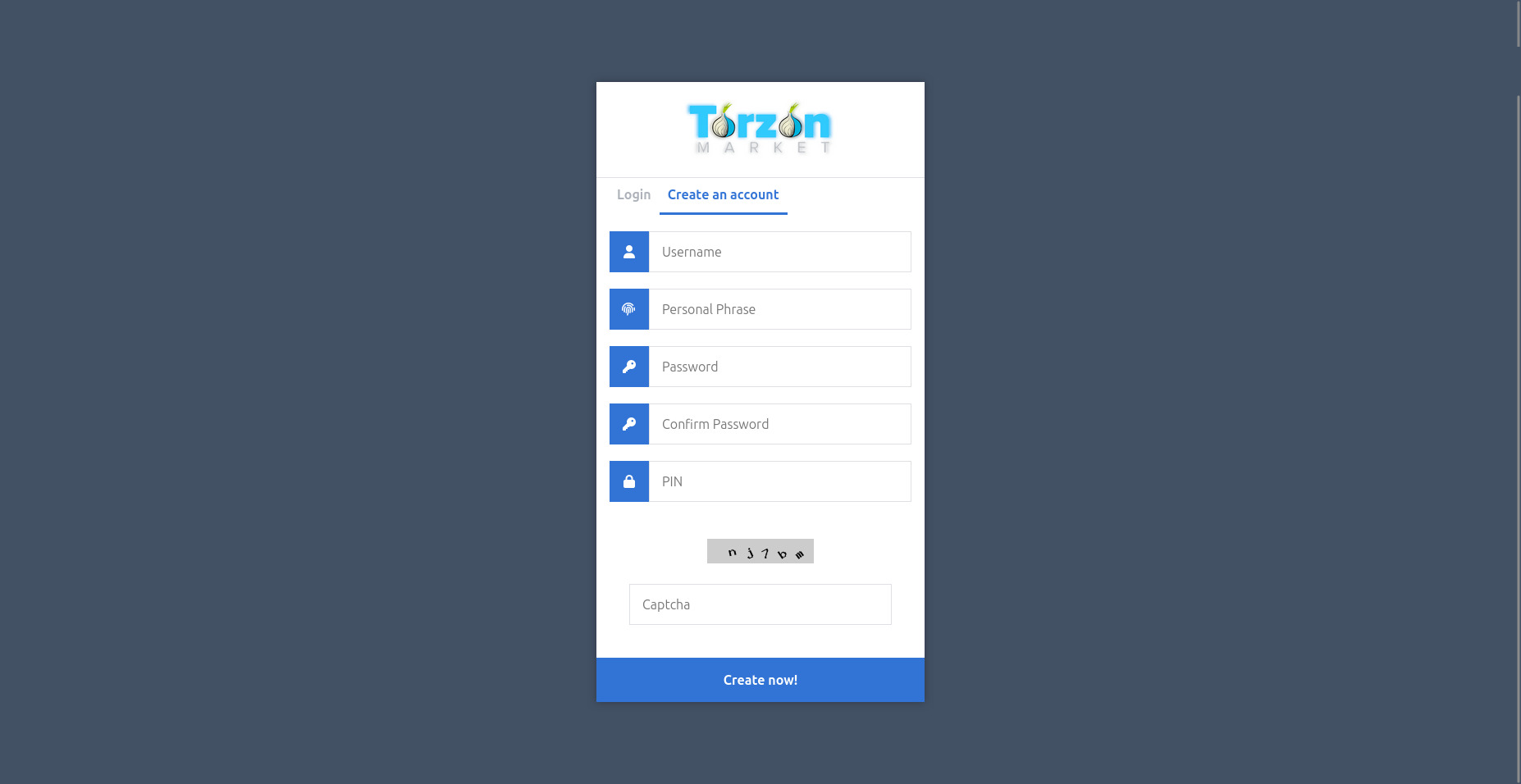
Fig 3. Account Registration Protocol
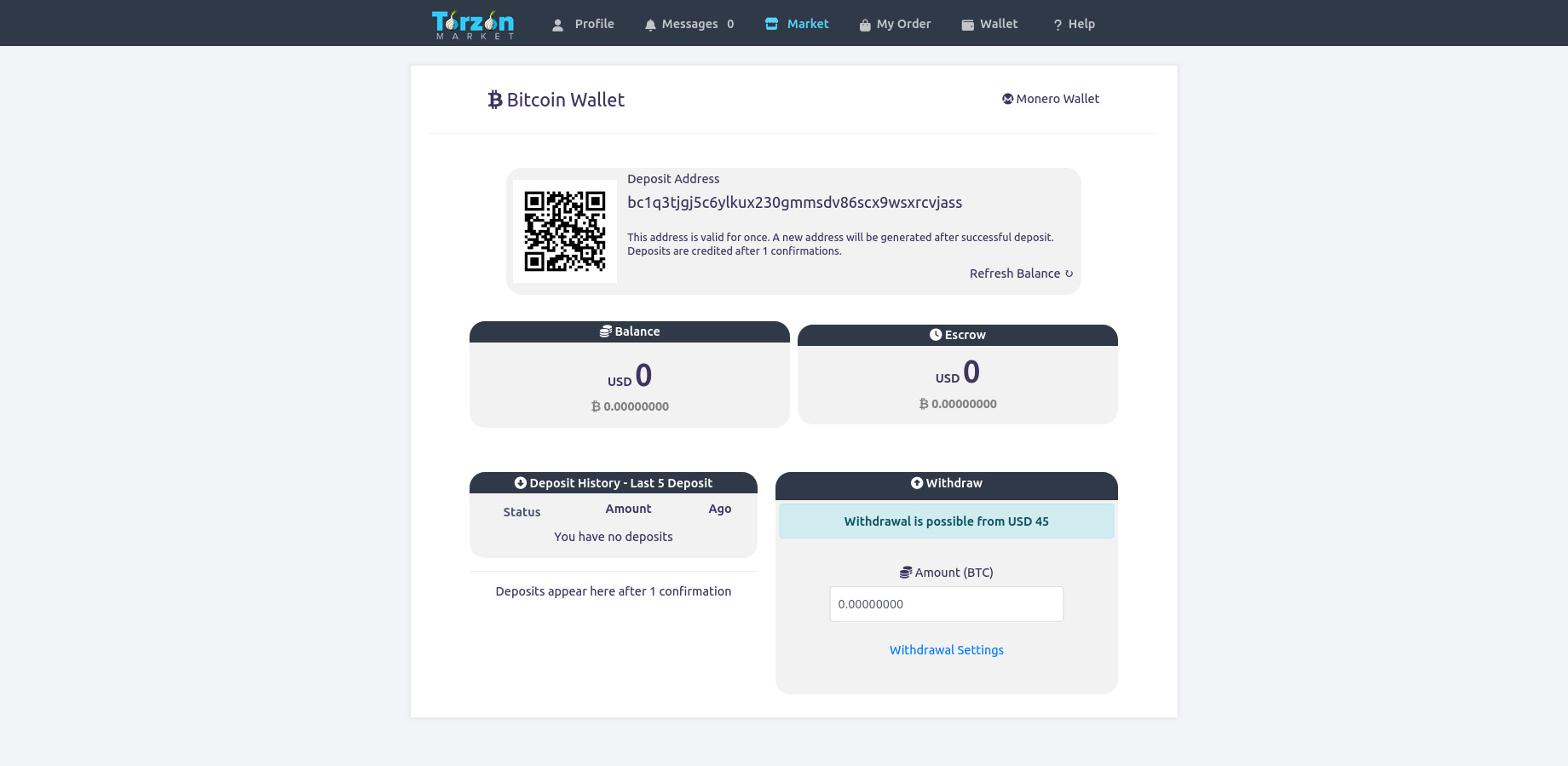
Fig 4. Main Infrastructure Dashboard
Community & Infrastructure Statistics
Network Observers
300k+
Supplier Bond Req.
Strict
Protocol Layer
v3 Deep Web
Active Categories
Digital Core
Analytical data suggests a consistent growth in network participants, driven largely by the mandatory application of cryptographic security measures. The administration enacts rigorous account verification prerequisites for suppliers, requiring substantial digital bonds to operate, thereby enforcing a self-regulating economic environment. Overall consensus among structural analysts points to an infrastructure designed for endurance and resilience against external network interference.